Key Takeaways
Social engineering attacks exploit trust, urgency, and confusion more than any fancy tech weakness.
The safest traders rely on simple processes, double-checking, and wallet separation instead of just trusting their gut.
Slowing down before you sign or approve anything is one of the strongest defenses you have in crypto.
Social engineering attacks trick people instead of breaking code. They play on trust, hurry, confusion, and the habit of clicking fast. These attacks pop up in Telegram, Discord, fake wallet pop-ups, email links, Zoom calls, and even token launch chats. They look completely normal until suddenly your wallet is lighter.
This guide walks you through exactly what these attacks look like today, shows the real patterns happening in 2026, and gives you easy, practical steps to protect yourself even when you feel stressed or rushed.
How Social Engineering Works: It Tricks Your Decisions, Not the Tech
The main idea is simple. Scammers do not always need to hack your wallet directly. If they can get you to sign, approve, connect, or share something risky, the damage is just as bad.
Here is a clear breakdown:
Attack Type | What It Targets |
Phishing link | Your trust in what looks normal |
Fake support request | Your belief in authority |
Urgent wallet warning | Your fear and need for speed |
Impersonation | Your habit of reacting to familiar names |
The key point is that you often become the weakest link when the actual tech gets harder to break.
The Most Common Tricks: Urgency, Authority, and Confusion
Scammers rarely rely on fancy words. They use feelings instead.
Manipulation Trick | Typical Signal Example |
Urgency | “Act now or your wallet will be frozen” |
Authority | “I’m from support” or “core team admin here” |
Confusion | “Just verify this contract or sync your wallet” |
These three usually team up. You feel pressured to move fast, you trust the person, and the tech talk makes you think you need their help. Most crypto scams are really just psychological scripts dressed up as normal instructions.
Real 2026 Attack Patterns
As crypto gets more advanced, scammers copy the new ways we use it. Common examples right now include:
Fake token claim pages that ask for approvals
Impersonated admins in DeFi groups
Fraudulent AI-agent setup guides asking for broad permissions
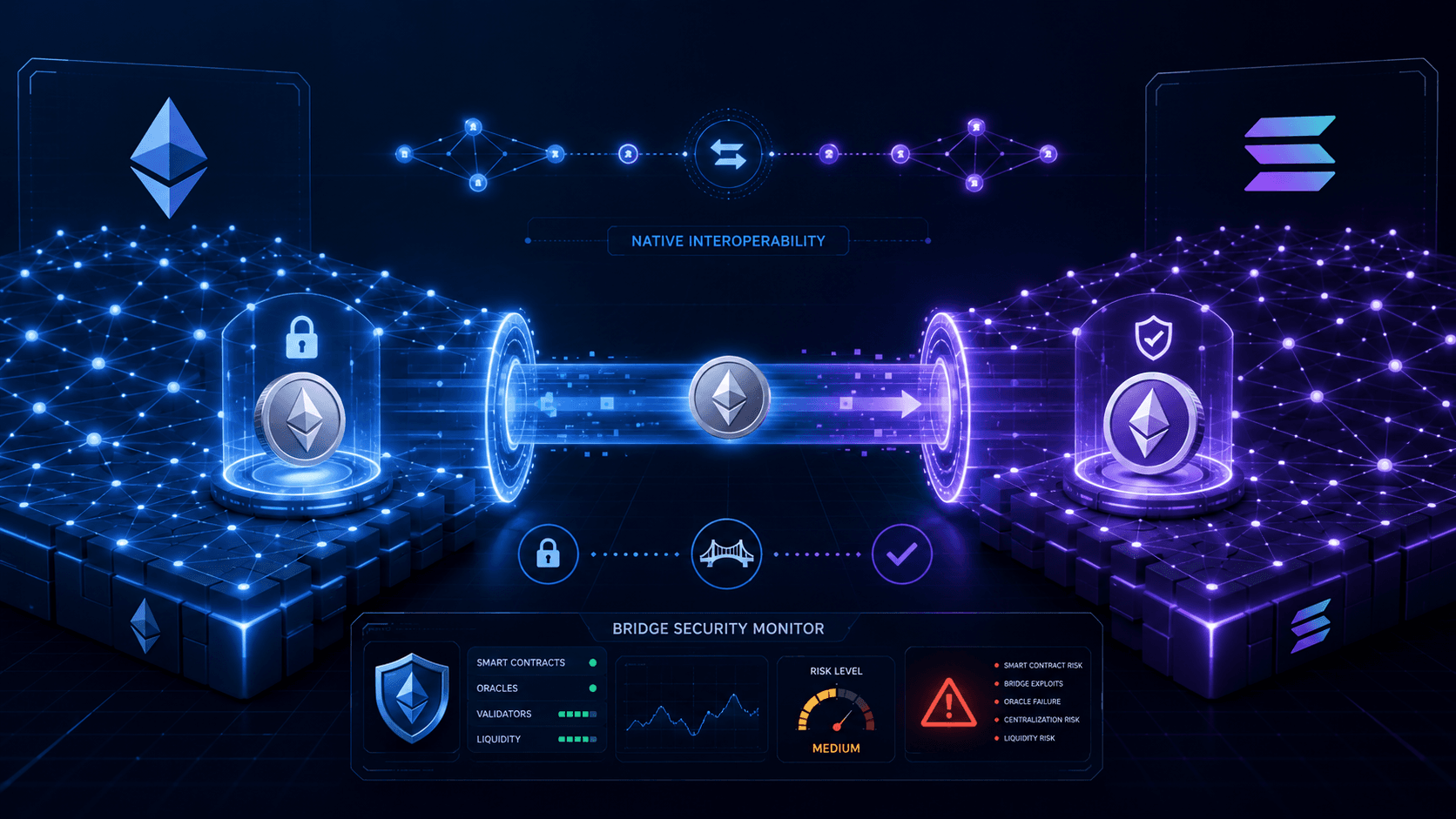
Fake bridge or airdrop websites
Targeted messages to protocol teams or treasury operators
The tricks evolve with new tools like bridges, dashboards, and multisig setups, but the old manipulation tricks stay exactly the same.
Why Wallet Approvals Are Still One of the Biggest Risks
Approvals are useful for trading and DeFi, but they can be dangerous if you do not understand them fully.
Approval-Related Scam | Why It Works So Well |
Fake airdrop claim | You expect to sign something normal |
Fake swap or bridge prompt | You think it is just a routine step |
“Security verification” request | You mistake it for a harmless confirmation |
Many beginners still mix up a simple signature, a token approval, and a dangerous full authorization. Scammers count on that confusion, so approval literacy is now one of the most important skills you can learn.
Why Support Impersonation Works So Well in Crypto
Crypto often feels confusing with new interfaces, failed transactions, and fast updates. That uncertainty makes people reach out for help, and scammers love stepping in as the helpful expert.
They exploit the fact that you already expect things to be a bit messy, so a friendly “support” message feels normal.
Good Defense Starts with Simple Habits, Not Being Super Smart
You do not need to be a genius to stay safe. You just need repeatable steps that work even when you are emotional or in a hurry.
Strong habits include:
Never clicking links sent by strangers for wallet actions
Always typing the website address yourself
Treating every direct message as untrusted until proven otherwise
Reviewing every signature and approval carefully before confirming
Using separate wallets for risky activities
These procedures beat instinct every time because instincts fail under pressure.
The Power of Small Wallet Separation
This is one of the easiest and most effective things you can do.
Wallet Role | Safer Use |
Cold storage wallet | Long-term holding, almost no daily interaction |
Active DeFi wallet | Everyday trading and limited-risk activities |
Experimental wallet | Airdrops, tests, and unknown new projects |
If something goes wrong in the experimental wallet, your main funds stay safe. This limits the cost of any single mistake.
Extra Tips for Team Operators and Higher-Value Wallets
The bigger your wallet or authority, the more attractive you become to scammers. Multisig signers, project admins, treasury operators, and public large holders get hit with fake calendar invites, urgent “coordination” messages, and private support requests.
For you, double-check everything and never shortcut verification.
Your Simple 2026 Defense Checklist
Good protection does not need to be complicated. Use this every time:
Defense Habit | Why It Works |
Verify links manually | Stops most phishing attempts |
Ignore unsolicited support DMs | Cuts off the most common authority scams |
Use wallet separation | Limits how much one mistake can cost you |
Recheck approvals before signing | Prevents easy authorization abuse |
Slow down under urgency | Breaks the scammer’s timing advantage |
Slowing down is not being scared. It is smart defense.
Final Thoughts
Social engineering is still one of the biggest threats in crypto because it attacks the human side, not just the code. In 2026, scammers have gotten better at copying normal workflows like airdrops, bridges, DeFi support, and AI setups.
The best protection is not paranoia. It is calm, disciplined habits: verify everything yourself, separate your wallets, treat random messages as untrusted, read approvals slowly, and never let urgency make decisions for you.
Most losses happen not because the scammer was brilliant, but because the trader was rushed. That is something you can fix starting today.
FAQ
It is a scam that tricks you into revealing access, signing dangerous approvals, or trusting fake support and websites.
A mix of urgency, fake authority, and confusing technical instructions that push you to act fast.
No. Advanced users, protocol teams, and large wallet holders get targeted too, especially when they control big assets or permissions.
Verify everything yourself, never rush because of a message or fear, and always use separate wallets for risky actions.
It limits the damage from one mistaken click or approval, so your main funds stay protected even if something goes wrong.
Disclaimer: This content is for educational and informational purposes only and is not financial advice. Nothing here is a recommendation to buy or sell any asset or use any platform. Do your own research and manage your risk.
Read More
Top 5 Paper Trading Platforms to Practice Crypto Trading Risk-Free
How to Track On-Chain AI Activity: Useful Dashboards and Beginner Opportunities in Networks Like Bittensor
Bittensor Subnet Drama and TAO Crash: Covenant AI Exit, Governance Concerns, and Lessons for Decentralized AI Participants